Which ports are occupied by which service? How many open ports are there? Learn to scan for open ports on your Linux system or any remote system.Table of Contents
- Method 1: Checking open ports in the currently logged in Linux system using lsof command
- Method 2: Checking ports on any remote Linux server using the netcat command
- Conclusion
Whether you are using Linux as a server or desktop, knowing open ports or ports in use can be helpful in a variety of situations.
For example, if you are running an Apache or Ngnix based web server, the port in use should be 80 or 443. Checking the ports will confirm that. Similarly, you can check which port is being used by SMTP or SSH or some other services. Knowing which ports are in use can be helpful while allocating the ports to a new service.
You may also check if there are open ports for intrusion detection.
There are various ways for checking ports in Linux. I’ll share two of my favorite methods in this quick tip.
Method 1: Checking open ports in the currently logged in Linux system using lsof command
If you are logged into a system, either directly or via SSH, you can use the lsof command to check its ports.
sudo lsof -i -P -n
This lsof command is used to find the files and processes used by a user. The options user here are:
- -i: If no IP address is specified, this option selects the listing of all network files
- -P: inhibits the conversion of port numbers to port names for network files
- -n: inhibits the conversion of network numbers to host names for network files
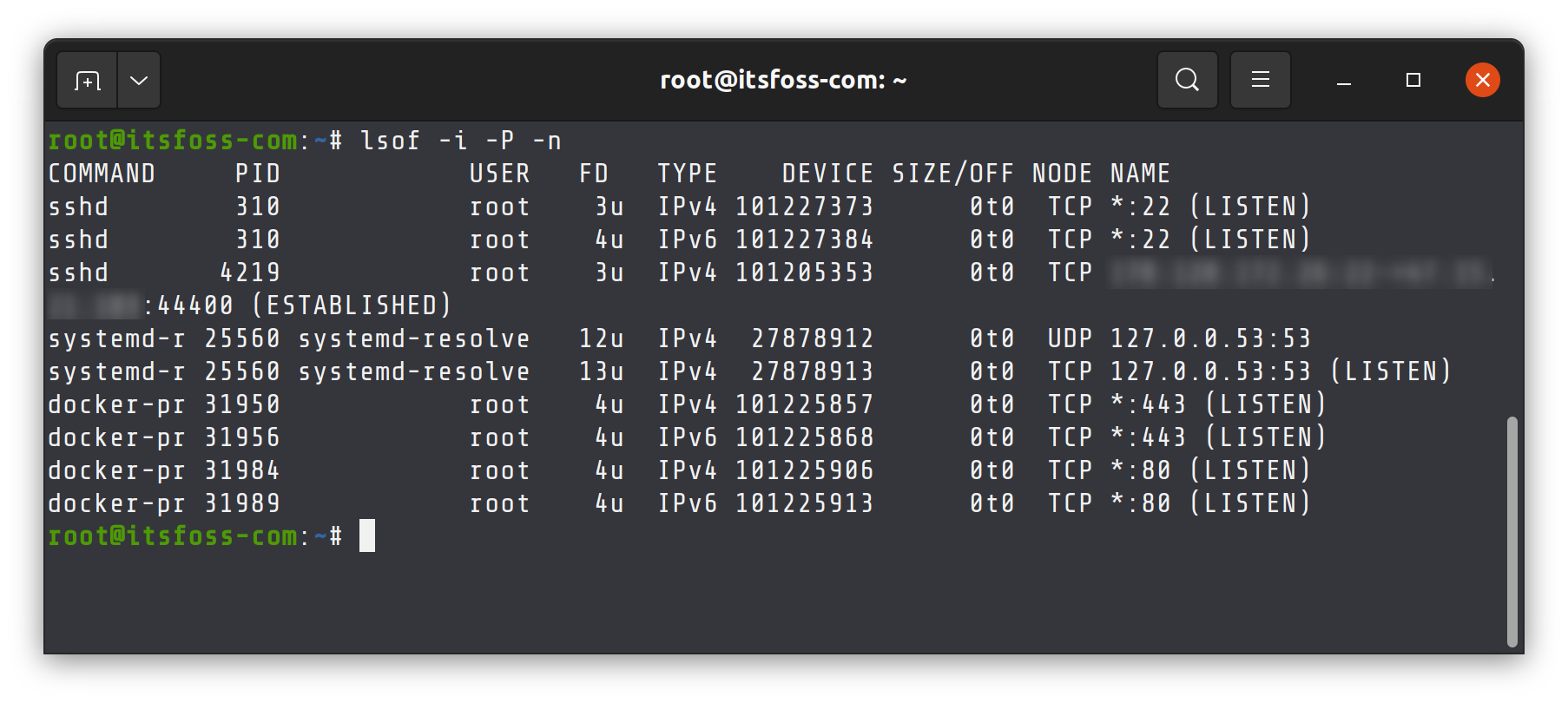
But, this also shows us a lot of extra ports that the computer does not actually listen to.
You can just pipe this output to the grep command and match the pattern “LISTEN”, like this:
sudo lsof -i -P -n | grep LISTEN
This will only show the ports that our computer is actively listening to and also which service is using said open port.
Method 2: Checking ports on any remote Linux server using the netcat command
nc (Netcat) is a command line utility that read and writes data between computers over network using the TCP and UDP protocols.
Given below is the syntax for nc command:
nc [options] host port
This utility has a nifty -z flag. When used, it will make nc scan for listening daemons without actually sending any data to the port.
Combine this with the -v flag, enabling verbosity, you can get a detailed output.
Below is the command you can use to scan for open ports using the nc command:
nc -z -v <IP-ADDRESS> 1-65535 2>&1 | grep -v 'Connection refused'
Replace IP-ADDRESS with the IP address of the Linux system you are checking the ports for.
As for why I selected values 1 to 65535, that is because the port range starts from 1 and ends at 65535.
Finally, pipe the output to the grep command. Using the -v option, it excludes any line that has “Connection refused” as a matched pattern.
This will show all the ports that are open on the computer which are accessible by another machine on the network.
Conclusion
Of the two methods, I prefer the lsof command. It’s quicker than nc command. However, you need to be logged into the system and have sudo access for that. In other words, lsof is more suitable a choice if you are managing a system.
The nc command has the flexibility of scanning ports without being logged in.
Both commands can be used for checking open ports in Linux based on the scenario you are in. Enjoy.TipsSHARE